Containers
Category: Learning Levels
Modernize Java and .NET applications remotely using AWS App2Container
Since the launch of AWS App2Container, customers have been asking for the ability to remotely manage the migrations of Java and .NET applications running on Windows or Linux hosts. Beginning with the version 1.2 of App2Container, users can accomplish containerization of their workloads without installing A2C software on the application servers. The remote execution feature […]
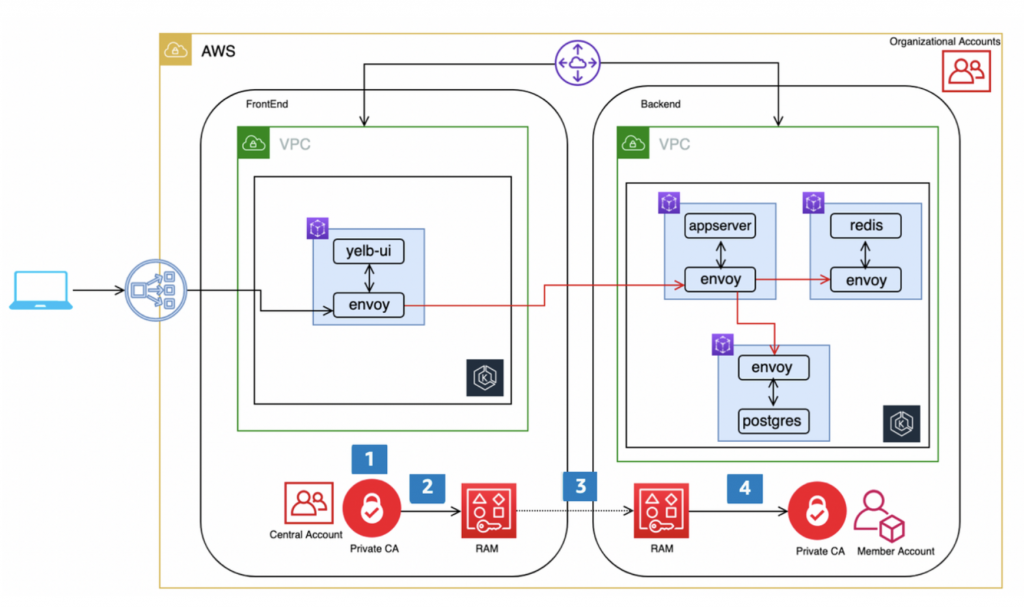
Traffic Encryption in AWS App Mesh across accounts using certificates from AWS Certificate Manager Private CA and AWS Resource Manager
NOTICE: October 04, 2024 – This post no longer reflects the best guidance for configuring a service mesh with Amazon ECS and Amazon EKS, and its examples no longer work as shown. For workloads running on Amazon ECS, please refer to newer content on Amazon ECS Service Connect, and for workloads running on Amazon EKS, […]
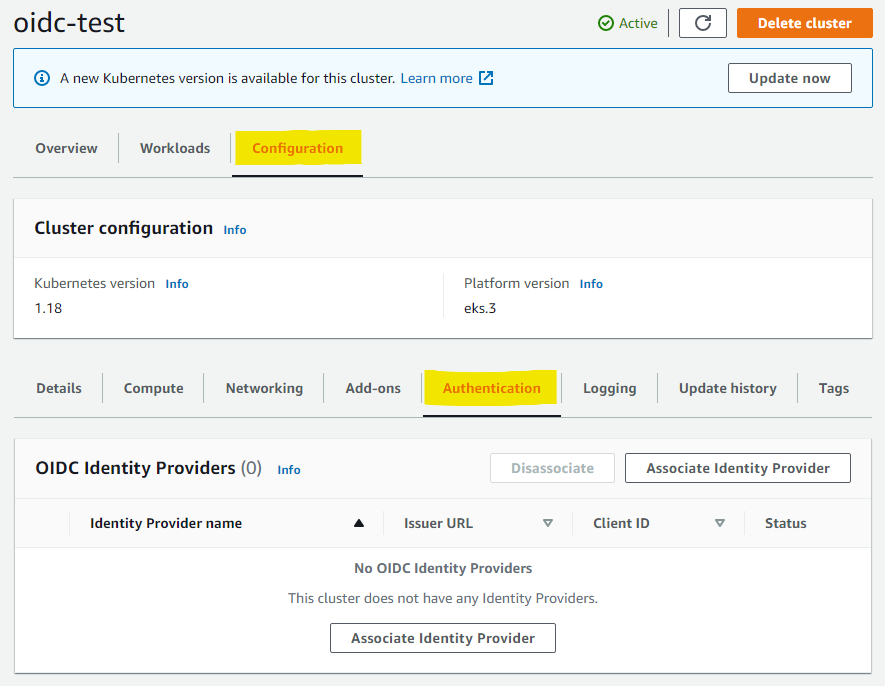
Introducing OIDC identity provider authentication for Amazon EKS
Today, we introduced user authentication for Amazon EKS clusters from an OpenID Connect (OIDC) Identity Provider (IDP). This feature allows customers to integrate an OIDC identity provider with a new or existing Amazon EKS cluster running Kubernetes version 1.16 or later. The OIDC IDP can be used as an alternative to, or along with AWS […]
Accelerate modernization of your application using App2Container
Introduction Many enterprises want to modernize their existing applications and containerize them to minimize disruptions that could stem from clunky, outdated and unscalable legacy systems. These enterprises need tools to simplify the containerization process of existing Java and .NET applications and increase operational efficiency, harmonize CI/CD processes, and increase agility. AWS App2Container (A2C) enables companies […]
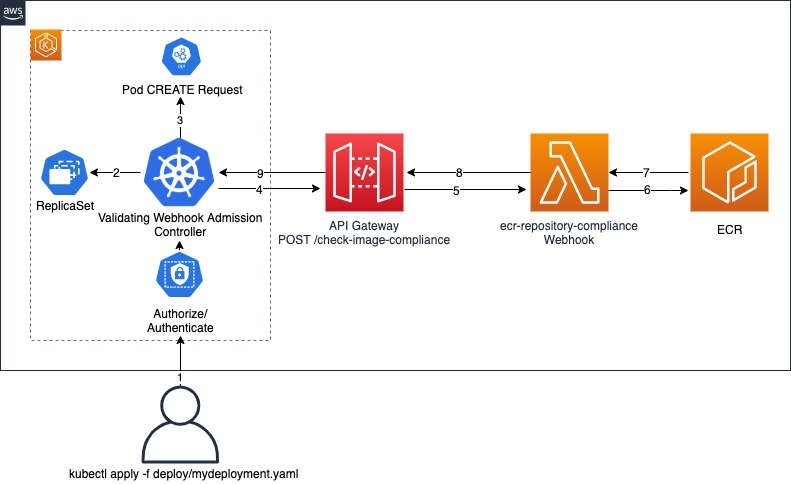
Building serverless admission webhooks for Kubernetes with AWS SAM
Authors: Simon Woldemichael, Associate Solutions Architect, WWPS Solution Architecture Josh Jiang, Associate Cloud Developer, Professional Services Shared Delivery Teams Learning Level: 300 Controlling resource deployments in your Kubernetes cluster can become a difficult challenge. For instance, pushing changes to a production environment can run the risk of installing an incompatible package or vulnerable dependency that […]
Enable traffic encryption between services in AWS App Mesh using AWS Certificate Manager or customer-provided certificates
NOTICE: October 04, 2024 – This post no longer reflects the best guidance for configuring a service mesh with Amazon ECS and Amazon EKS, and its examples no longer work as shown. For workloads running on Amazon ECS, please refer to newer content on Amazon ECS Service Connect, and for workloads running on Amazon EKS, […]
Access Logging Made Easy with AWS App Mesh and Fluent Bit
NOTICE: October 04, 2024 – This post no longer reflects the best guidance for configuring a service mesh with Amazon ECS and Amazon EKS, and its examples no longer work as shown. For workloads running on Amazon ECS, please refer to newer content on Amazon ECS Service Connect, and for workloads running on Amazon EKS, […]
AWS CodeDeploy now supports linear and canary deployments for Amazon ECS
AWS CodeDeploy has extended blue/green deployment support for Elastic Container Service (Amazon ECS) to include canary and linear deployments for applications hosted on AWS Fargate or Amazon Compute Cloud (Amazon EC2). Blue/green deployments are a safe deployment strategy provided by AWS CodeDeploy for minimizing interruptions caused by changing application versions. This is accomplished by creating […]
How to use Multiple load balancer Target Group Support for Amazon ECS to access internal and external service endpoint using the same DNS name
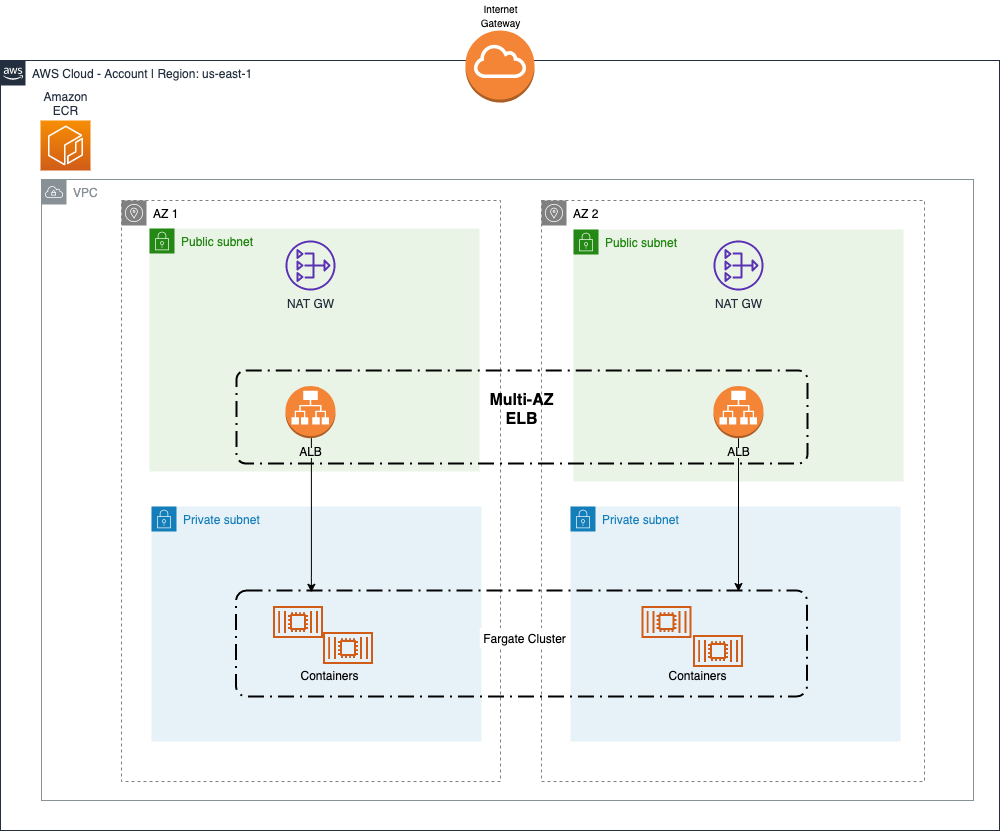
Customers running container-based applications on Amazon ECS using Amazon EC2 (commonly referred to as EC2) or AWS Fargate, frequently need to expose the application to both external clients and internal clients within the Amazon VPC (commonly referred to as VPC). In this blog post, we will look at a solution to optimize cost and reduce […]
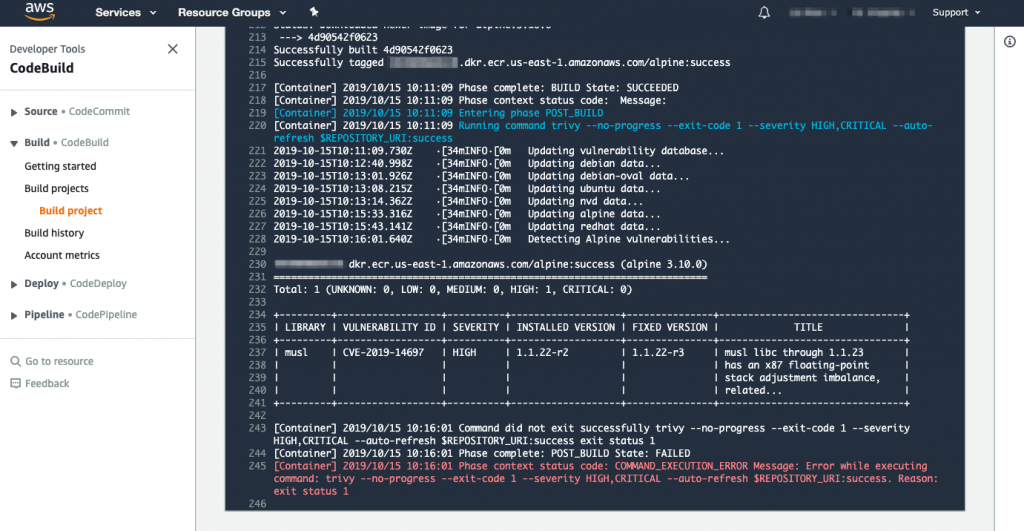
Scanning images with Trivy in an AWS CodePipeline
This post was contributed by AWS Container Hero, Liz Rice, VP Open Source Engineering at Aqua Security. If you’re working with containers, it’s important to scan your images for known vulnerabilities, so that you don’t deploy code that an attacker can easily exploit. A good way of ensuring that all your deployed images get this […]